Empowering Cloud Security: Explore FatPipe SD-WAN’s ‘Bring Your Own Firewall’ Advantage
 In today’s evolving landscape of digital transformation, the path to adopting Secure Access Service Edge (SASE) varies widely depending on the organization, reflecting the unique circumstances and objectives of each entity embarking on this transformative journey. At FatPipe, we recognize the unique nature of every SASE transition. We understand that each organization starts this journey from a different starting point, which highlights the importance of a flexible approach that delivers tangible benefits at every step.
In today’s evolving landscape of digital transformation, the path to adopting Secure Access Service Edge (SASE) varies widely depending on the organization, reflecting the unique circumstances and objectives of each entity embarking on this transformative journey. At FatPipe, we recognize the unique nature of every SASE transition. We understand that each organization starts this journey from a different starting point, which highlights the importance of a flexible approach that delivers tangible benefits at every step.
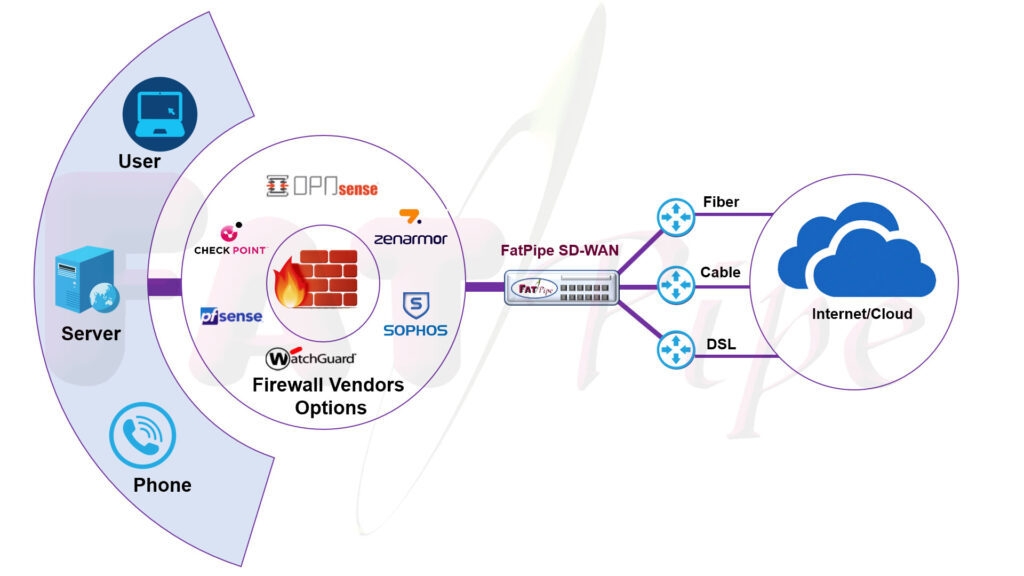
Flexibility isn’t just about incremental wins; it’s about empowering organizations to adapt and evolve on their terms. FatPipe follows a flexible approach that not only acknowledges but embraces the diverse needs and circumstances of our customers. At FatPipe, we have innovated our SD-WAN solutions with a third-party Bring Your Own Firewall (BYOF) model to provide organizations with unparalleled flexibility and choice in their security infrastructure. This approach allows organizations to leverage their preferred firewall technology within FatPipe’s SASE framework, creating a cohesive and robust security environment tailored to their specific needs.
Benefits of FatPipe SD-WAN Bring your own Line and Bring Your Own Firewall Integration
- The integration between FatPipe SD-WAN and third-party firewalls is developed to facilitate a smooth and efficient flow of traffic within the SASE architecture. By seamlessly integrating these elements, organizations can ensure that their network traffic is routed through their chosen firewall for inspection and enforcement of security policies. This integration streamlines security operations and ensures consistent protection across the entire network infrastructure.
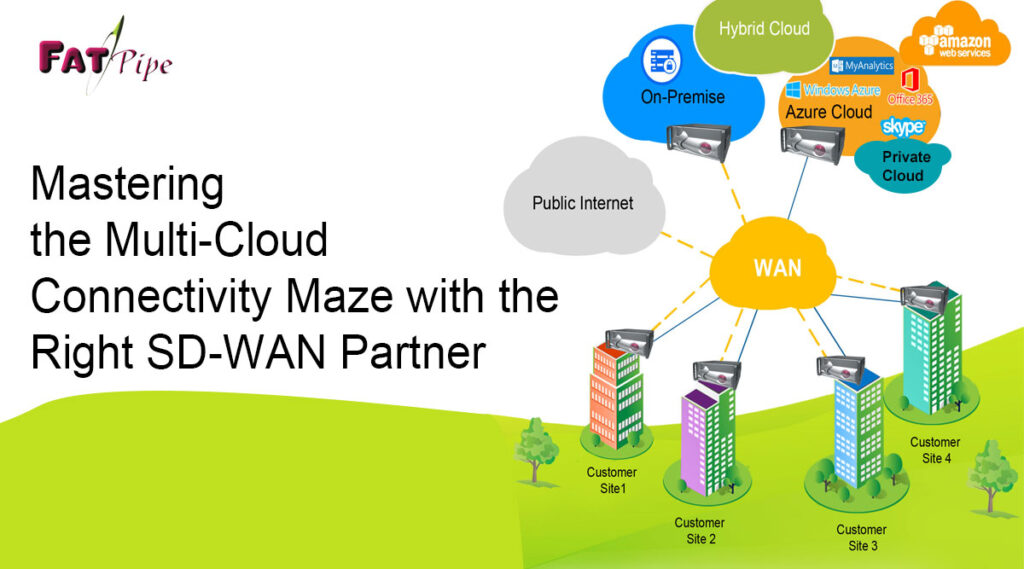
- Within the SASE framework, FatPipe’s SD-WAN acts as the foundation for connectivity, providing feature of “Bring your own line” which allows seamless aggregated connectivity across heterogeneous media types e.g., Wireless, Wireline, MPLS, Internet, 4G/5G etc. The third-party firewall, brought in by the organization under the BYOF model, serves as an additional layer of defense, augmenting the security capabilities of the SD-WAN solution. Together, these components work in tandem to safeguard against a wide spectrum of threats and vulnerabilities, ensuring comprehensive protection for the organization’s digital assets.
- This integrated approach not only enhances security but also provides higher Network Uptimes with seamless integration of heterogeneous lines with simple administration for IT teams. By consolidating networking and security functions within a unified platform, organizations can reduce complexity, streamline operations, and improve overall efficiency. Moreover, the flexibility offered by the BYOF and BYOL model enables organizations to leverage their existing investments in security infrastructure, maximizing ROI while benefiting from the advanced capabilities of FatPipe’s SASE-enabled SD-WAN solution.